Startup marketing, billing, pricing, AI monetization by Arnon Shimoni
-
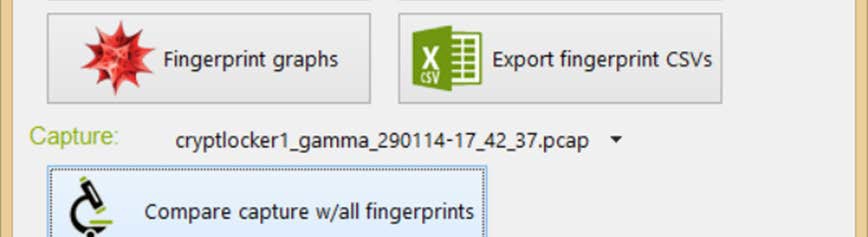
Malicious traffic detection using traffic fingerprints and machine learning
Over the past year, we’ve worked on a machine learning project at Ben Gurion University of the Negev. The project attempted to find out if we can identify malicious underlying traffic (viruses, botnets, command and control channels) hiding interspersed in ‘normal’ network traffic, without using advanced heuristics or deep packet inspection – but by using… -

I’ve managed to compile GHC-7.8.3 on an Nvidia Tegra (Jetson K1) and Adapteva Parallella-16!
It took a while, but I’ve finally managed to compile and run GHC-7.8.3 on an Nvidia Jetson K1 board. The Jetson K1 board has a 32-bit Nvidia Tegra processor (essentially a quad-core ARM Cortex A15), and an integrated 192 core Nvidia GPU. Mine came with a standard Ubuntu 14.04 distribution and nothing more really. After… -
Rot13 implementation in Haskell
Rot13 is a simple Caeser-cypher where letters are replaced by shifting them by 13 places. > import Data.Maybe (fromMaybe) > rot13 :: String -> String > rot13 s = map rotchar s > where we’ll first look in the lowercase letters > rotchar c = case (lookup c $ transp lc) of > Just x…